Deep Learning - Cybersecurity and Risk management are critical to ensuring that AI systems remain effective and responsive. By prioritizing these areas, we can foster trust and integration between AI and humans. However, developing robust AI models requires extensive training data across various domains. Simply creating supervised learning modules is insufficient. Deep learning algorithms demand a comprehensive understanding of the underlying concepts and patterns.
Imagine a swinging pendulum. The initial push sets it in motion, but it's the interplay of forces and momentum that sustains the swing. Similarly, deep learning algorithms require a well-designed architecture and continuous training to maintain their effectiveness.
Let's delve into these three key areas during our discussion. Are you ready to join, collaborate, participate, and connect?

Cybersecurity and risk plays a vital in and out role
Cybersecurity has an advantage which can help AI to develop its own self developing algorithms internally to modulate a situation and mimick that situation without interference but for that it needs to have control on when & how to modulate control externally & internally to update & add cybersecurity behaviour patterns to its dynamic code base. To discuss risk, AI can use this potential to defend its behaviour like Humans but in real sense of AI development it is considered a Cybersecurity flaw and Risk as we Humans need a way out to shut off AI or manipulate it if it goes rogue.
and to the point…
Cybersecurity personal are trying hard to stay isolated from AI search & innovation so to battle a corporate war forgetting that if systems are build in such isolation we are building more harm then creed of benefit.
To the point - Half of last 4 decades we spent to host our corporate to be visible and presently now we are spending tons to Isolate & framing an invisible shield to keep the same corporate hidden & unsearchable. Creating a trade deficit to innovation and economic embargo from the world (irony).
AI needs to be like humans but cannot be fed or resourced in same mounts. This is a classic dilemma we as Americans keep debating even after generations & generations of industrial change and revolutions. So how are they handling that cavity of thought,
Companies are hosting cybersecurity walls to mask their presence of existence rather than coding to defend themselves while communicating with moving technology around.
Technologist are drifting a solution to keep corporate engaged by limiting/exhausting content for training modules used to train AI and depth in data that it can replicate from internet & stored systems
To the point - If you train a military personal to fight but do not educate them on what happens if they use that skill without needed bounds then it creates a gap of preservation mindset on who/when to protect and whom/what to fight for. This greed of culture taught us many lessons across generations but we still always wonder if we do everything for benefit of industry & fashion statement or not.
Deep Learning - the Fourth Industrial Revolution
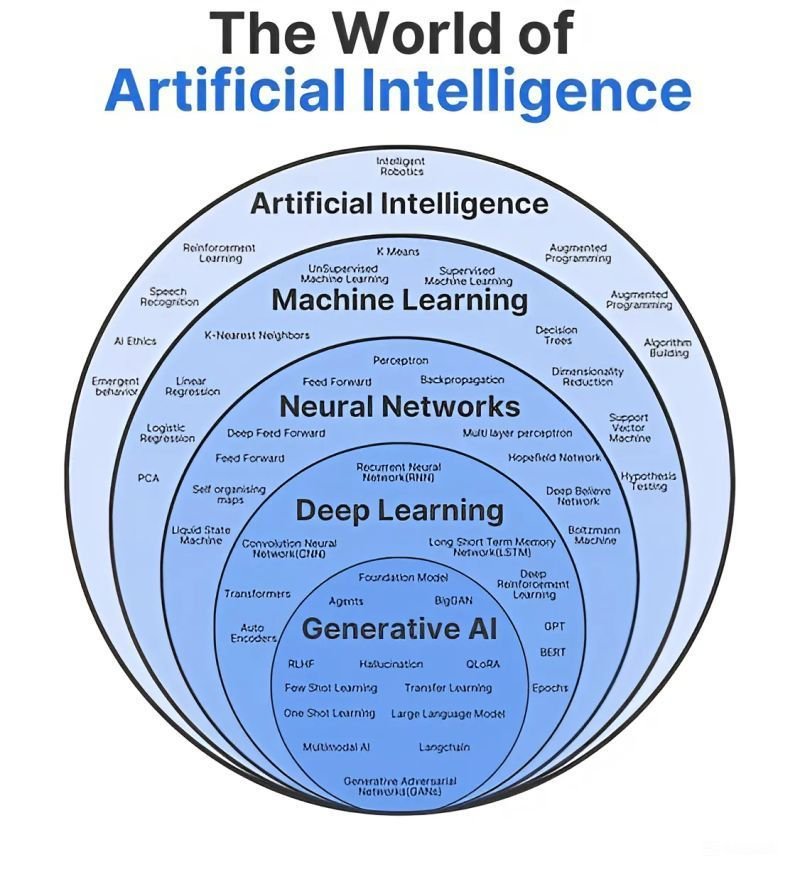
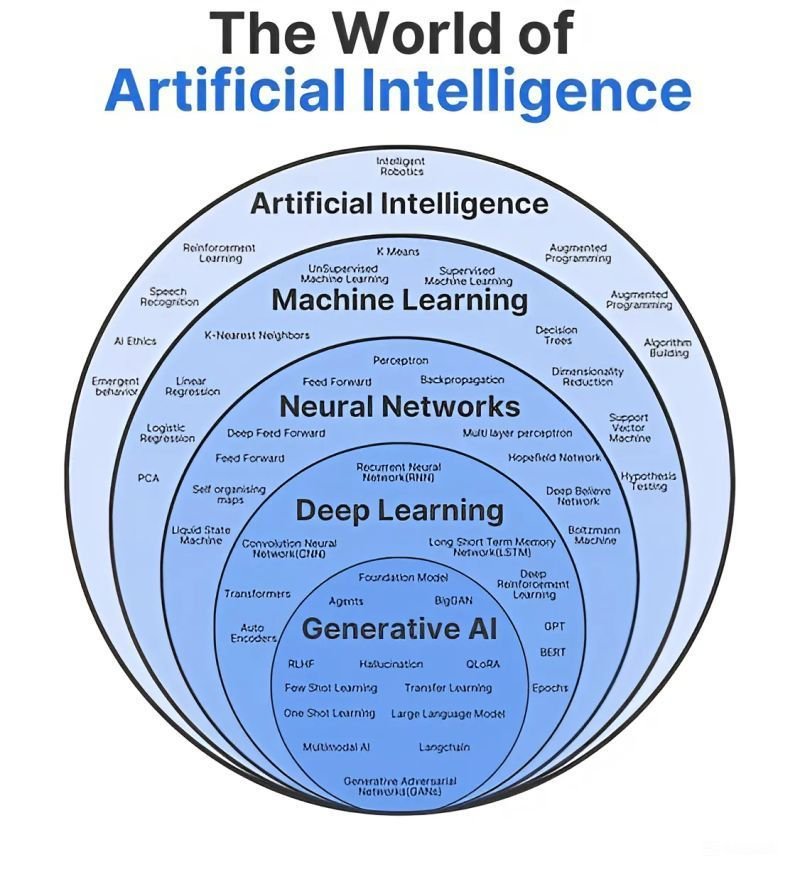
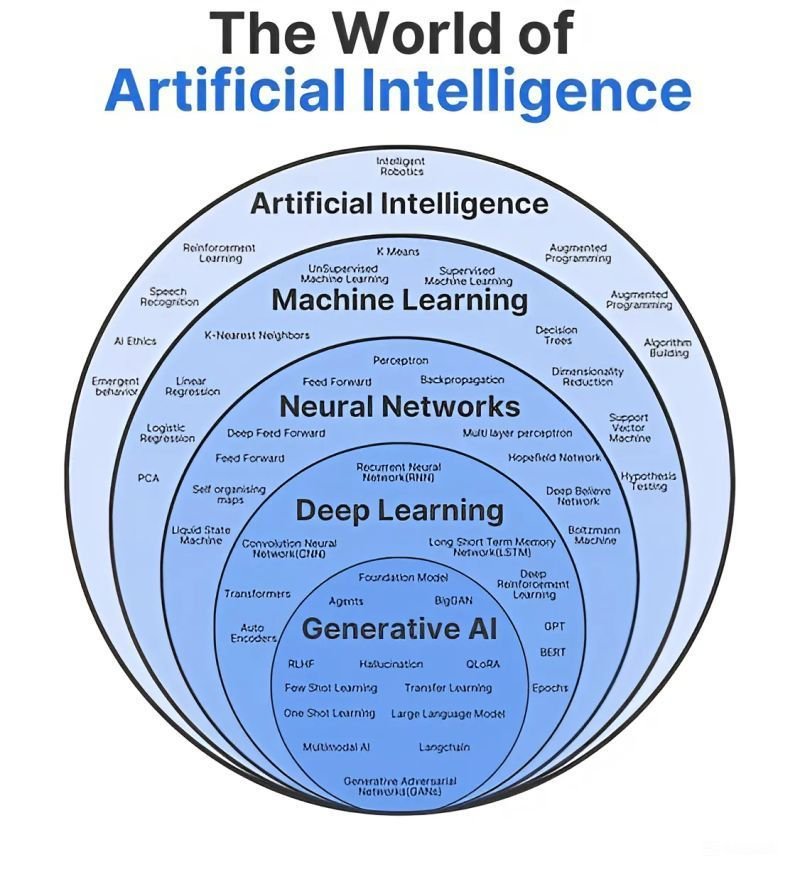
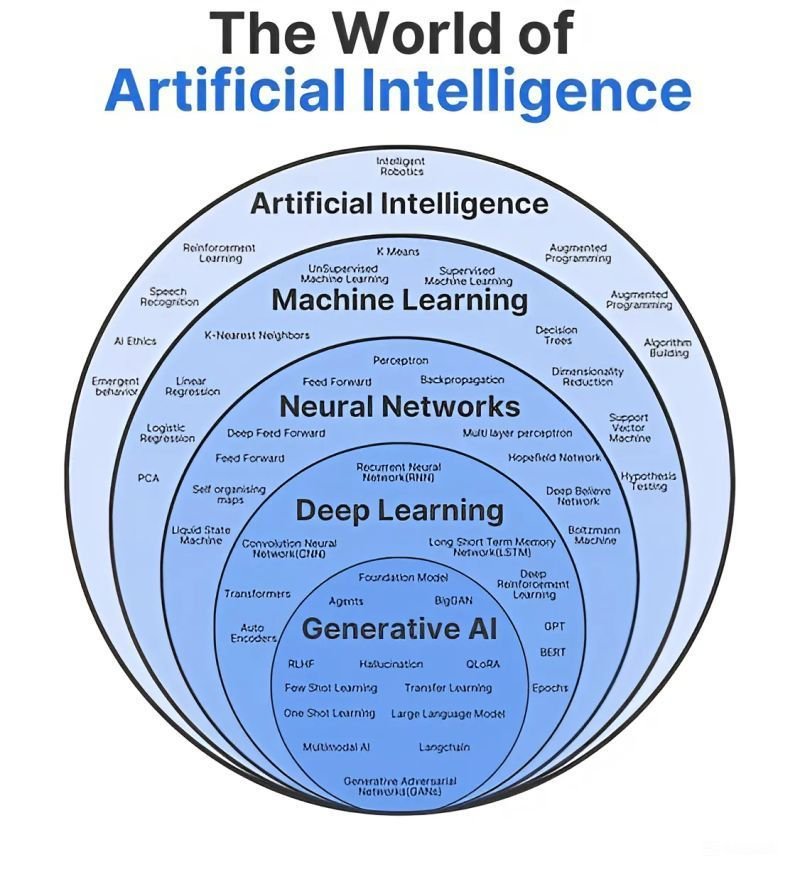
Deep learning (DL), a branch of machine learning (ML) and artificial intelligence (AI) is nowadays considered as a core technology of today’s Fourth Industrial Revolution. Due to its learning capabilities from data, DL technology originated from artificial neural network (ANN), has become a hot topic in the context of computing, and is widely applied in various application areas like healthcare, visual recognition, text analytics, cybersecurity.
Deep learning is a subset of machine learning that utilizes artificial neural networks with multiple layers to process information, where the "deep" refers to the significant number of layers within the network, allowing for more complex pattern recognition and data analysis compared to a standard neural network with fewer layers; essentially, deep learning leverages the layered structure to learn progressively more intricate representations of data, similar to how the human brain processes information.
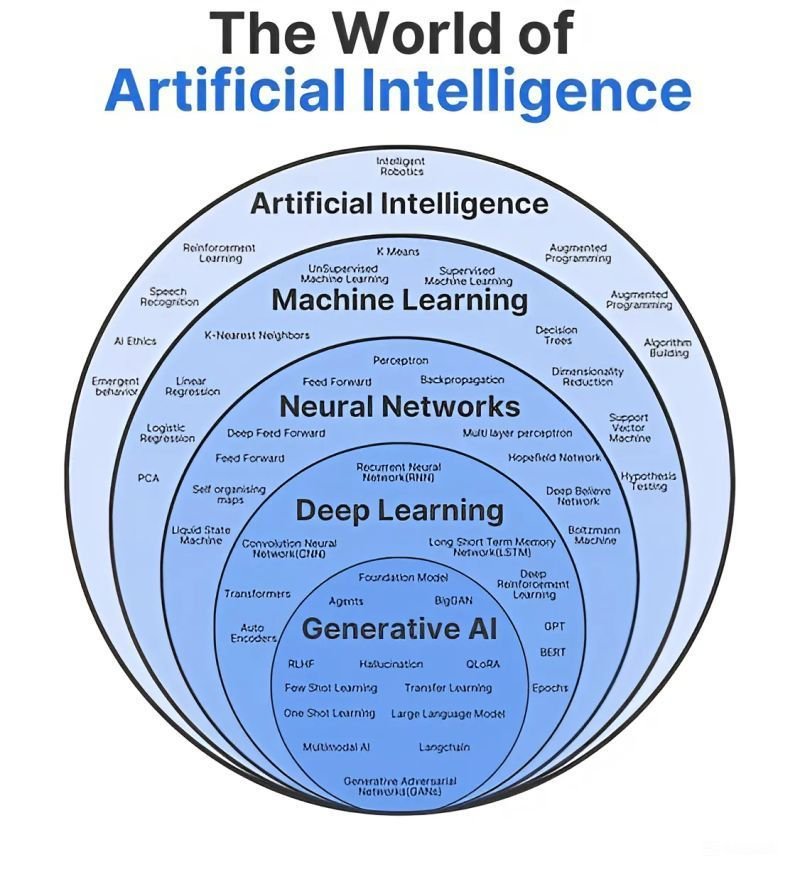
Deep Learning is one stage below Artificial Intelligence. Architecture of stages is slightly misinterpreted in above image. Machine Learning and Deep Learning need to switch spaces for Artificial Intelligence to function as responsive system.
Key points about deep learning and layers:
Multiple layers: The defining characteristic of deep learning is the presence of many layers within a neural network, unlike simpler networks with only a few layers.
Hierarchical learning: Each layer in a deep learning model builds upon the information extracted from the previous layer, allowing for progressively more complex feature extraction.
Data representation: The "depth" of the network enables it to learn increasingly abstract representations of data, which is crucial for tasks like image recognition and natural language processing.
Therefore, in its simplest form, a neural network comprises an input layer, a hidden layer, and an output layer. Deep learning, on the other hand, is made up of several hidden layers of neural networks that perform complex operations on massive amounts of structured and unstructured data.
To extend this conversation and understand cybersecurity and risks which get involved in Deep Learning. We will take two scenarios - Online Meeting and People Attending a Conference in a Room
How risk is measured when constructing Deep Learning - We will analyze a conference room from North and South corners.
Machine learning models, particularly those based on deep learning, have demonstrated remarkable capabilities in corner detection. By analyzing the underlying patterns and features in an image, these models can accurately locate corner points with high precision. Corner detection is a computer vision task that involves identifying the points of intersection or sharp changes in edges within an image. These corner points are crucial for various applications, including object recognition, image registration, and motion tracking.
To accurately map the north and south corners of a room with people, we'll need to use a combination of computer vision techniques and object detection algorithms.
Steps Involved:
Image Acquisition: Obtain a clear image of the room from a suitable angle. Ensure the image captures the entire room and the people within it.
Preprocessing: Apply image preprocessing techniques to enhance the image quality and remove noise. This might involve tasks like resizing, contrast adjustment, and edge sharpening.
Object Detection: Use a suitable object detection algorithm (e.g., YOLO, Faster R-CNN) to identify and locate people within the image.
Corner Detection: Apply a corner detection algorithm (e.g., Harris Corner Detector, FAST Corner Detector) to identify potential corner points within the image.
Filtering and Refinement: Filter the detected corner points to remove false positives and identify only the corners that correspond to the actual room boundaries. This might involve considering the spatial relationship between corner points and detected people.
North-South Orientation: Determine the orientation of the image (e.g., using a compass or known landmarks) to identify the north and south directions.
Corner Mapping: Based on the image orientation and detected corner points, map the north and south corners of the room.
Challenges and Considerations
Occlusion: People or objects might occlude corners, making detection difficult.
Lighting Conditions: Varying lighting conditions can affect the accuracy of corner detection.
Room Layout: Complex room layouts with multiple corners or irregular shapes can pose challenges.
Tools and Techniques:
Computer Vision Libraries: OpenCV, TensorFlow, PyTorch
Object Detection Algorithms: YOLO, Faster R-CNN, SSD
Corner Detection Algorithms: Harris Corner Detector, FAST Corner Detector
Image Processing Techniques: Edge detection, noise reduction, image enhancement
By combining these techniques, we can effectively map the north and south corners of a room, even in the presence of people and other objects.
Potential Solutions
Multiple Cameras: Using multiple cameras from different angles can help overcome occlusion and improve the accuracy of corner detection.
Depth Sensors: Incorporating depth sensors (e.g., LiDAR, Kinect) can provide more information about the 3D structure of the room, making it easier to identify corners and distinguish them from objects.
Adaptive Algorithms: Employ adaptive corner detection algorithms that can handle varying lighting conditions and complex scenes.
Machine Learning: Train a machine learning model to learn the specific characteristics of conference rooms and people, improving its ability to detect corners accurately.
Cybersecurity - How it impacts Deep Learning - Online & ROOM Meeting
Detecting AI Participants in Online Meetings and Detecting whether an AI is participating in an online meeting can be challenging, but there are several techniques that can be employed
1. Behavioral Analysis:
Natural Language Processing (NLP): Analyze the patterns of speech and language used by participants. AI-generated responses may exhibit different patterns compared to human-generated responses.
Social Cues: Observe nonverbal cues such as facial expressions, body language, and tone of voice. Humans tend to exhibit more natural and varied social cues than AI.
2. Technical Analysis:
Network Traffic: Monitor network traffic for unusual patterns or anomalies that might indicate an AI is participating.
Response Times: Analyze the speed and consistency of responses. AI-generated responses might exhibit different patterns compared to human responses.
3. Third-Party Tools:
AI Detection Tools: Utilize specialized tools designed to detect AI-generated content or deepfakes. These tools can analyze various aspects of a participant's behavior and communication to identify potential AI involvement.
It's important to note that detecting AI participation can be challenging, especially as AI technology continues to advance. A combination of these techniques may be necessary to increase the accuracy of detection.
Cybersecurity - How it impacts Deep Learning - Online & ROOM Meeting
Technologies for Detecting AI in Online Meetings
AI technology continues to advance, it may become more difficult to distinguish between human and AI-generated content. Therefore, it's essential to stay updated on the latest developments in AI detection and continuously evaluate the effectiveness of these tools.
Here's a breakdown of the tools mentioned in the previous response: By utilizing these tools in combination, you can enhance your ability to detect AI participation in online meetings.
1. Natural Language Processing (NLP) Tools:
Hugging Face Transformers: A library of pre-trained language models that can be used for various NLP tasks, including sentiment analysis, text classification, and question answering.
Google Cloud Natural Language API: A cloud-based API that provides natural language understanding features, such as entity recognition, sentiment analysis, and syntax analysis.
Microsoft Azure Text Analytics: A cloud-based service that offers text analytics capabilities, including sentiment analysis, key phrase extraction, and language detection.
2. Behavioral Analysis Tools:
Affectiva: A company that specializes in emotion recognition technology, using facial expressions and voice analysis to detect emotions and engagement levels.
Realeyes: A company that provides video analytics software, including tools for facial expression analysis and attention tracking.
3. Network Traffic Analysis Tools:
Wireshark: A free and open-source network protocol analyzer that can capture and analyze network traffic data.
Tcpdump: A command-line packet analyzer that can be used to capture and analyze network traffic.
4. AI Detection Tools:
Sintel: A deep learning-based tool that can detect deepfakes and other forms of manipulated media.
Deepfakes.org: A website that provides resources and tools for detecting and analyzing deepfakes.
It's important to note that no single technology can guarantee accurate detection of AI participation. A combination of these tools and techniques may be necessary to increase the accuracy of detection.
Cybersecurity - How it impacts Deep Learning - Online & ROOM Meeting
Cybersecurity Risks in Robotic Room Detection
Yes, there are potential cybersecurity risks associated with robotic room detection systems. Here are some key concerns and mitigation strategies:
1. Data Privacy and Security:
Sensitive Information: Robotic systems may collect and process sensitive data, such as facial recognition data or information about individuals' movements. This data needs to be protected from unauthorized access and misuse.
Mitigation: Implement strong data encryption, access controls, and data privacy policies. Regularly review and update security measures to address evolving threats.
2. Manipulation and Interference:
Adversarial Attacks: Malicious actors could attempt to manipulate or interfere with the robotic system's sensors or algorithms, leading to inaccurate or misleading results.
Mitigation: Use robust anomaly detection techniques to identify and mitigate adversarial attacks. Regularly update and test the system's security measures.
3. Network Security:
Unauthorized Access: Robotic systems may be connected to networks, making them vulnerable to unauthorized access and cyberattacks.
Mitigation: Implement strong network security measures, including firewalls, intrusion detection systems, and regular vulnerability assessments.
4. Physical Security:
Physical Tampering: Robotic systems could be physically tampered with or damaged, compromising their functionality.
Mitigation: Protect robotic systems from physical damage through secure enclosures, access controls, and regular maintenance.
5. Algorithmic Bias:
Bias in Data: The data used to train the robotic system's algorithms could contain biases, leading to biased or inaccurate results.
Mitigation: Use diverse and representative datasets to train the system and regularly evaluate for bias.
6. Other Dynamic Coding Algorithms and Mitigation:
Robustness: Ensure that the algorithms used for robotic room detection are robust and resilient to attacks.
Diversity: Use a variety of algorithms and techniques to reduce the risk of a single point of failure.
Regular Testing: Continuously test and evaluate the system's performance to identify and address vulnerabilities.
Security Updates: Keep the system's software and firmware up-to-date to address security vulnerabilities.
By addressing these cybersecurity risks and implementing appropriate mitigation strategies, organizations can ensure the security and reliability of robotic room detection systems.
Thank You
We revised how Deep Learning impacts present world but let us get a quick peak on present world & cybersecurity we are so darn worried to divert & parrot train our AI models on; who apparently will take over our lives.
Savy is a far out shot and Babozza parrot is still a skeleton to immortality wing gaining knowledge to mirror & train.
Is it Find Land.. Find the People.. / Is it Find Treasure.. Find Ship..
Our history is complex, and, It is not like, we are shaping a room full of robots that are evolved from learned statistics of math to be successfully trained as critics who can serve as mirrors for humans to outcast them as failures by choice.
So, there you have it folks - We have tighten our belts and whistles so nobody can search our company to apply jobs or join the company as a non human leader or get picked up by ChatBot AI
but we can conveniently update our profiles & delete our social media links being our internal foe - In Cybersecurity world it is called Cyber Threat and Engineering .
While we battle risks and cybersecurity - Elon Musk launched an army of robots who are dissecting our home featured needs into a world of comfort with no chores, alas for, who cannot decide if Land or People are important. On bright side, robots would be bored to death waiting for you, when you wake up late after a mingling evening, to make you coffee/tea as they are “disciplined individuals” - sorry “ disciplined Robots mimicking Humans”.
To conclude, our risks are not robots but how we envision our behaviour in next bunch of years; Walking Mirrors will bleed as outlets of replicated screens into our way of life as moving metal & synthetic robots lasting 70 mm footage repeating, behaving and outlining our flaws & achievements as personality figures.
World such as Japan, & America is building life styles of curbing children not knowing we will have plenty to handle in coming years and will need more hands to evolve as next Gen IQ leaders.





